Recently, Arm released a series of IP to protect the chip from physical attacks. This series extends Arm's secure IP product portfolio and provides physical security for all IoT products. These new IP products are marked with the letter “P†that stands for physical security, including the Cortex-M35P processor and a new set of security IPs (CryptoIsland-300P and CryptoCell-312P) that can prevent side channel attacks.
This article will explore how the Cortex-M35P offers tamper-resistant protection and protection against physical attacks against a broad, user-friendly Cortex-M processor with its advantages and features, thereby providing your product with the opportunity to enter new markets.
 The main advantages of Cortex-M35P
The main advantages of Cortex-M35P
The Cortex-M35P is the first Armv8-M processor to offer anti-tampering capabilities, making it easier and faster for processor cores to obtain payment-level or carrier-grade security certifications. The Cortex-M35P is also a processor with a multi-layer security architecture that combines software protection with Arm TrustZone technology and physical protection in the SecurCore family of processors. The Cortex-M35P is an extension of Arm's security portfolio and follows Arm's PSA platform security architecture principles.
| Make your design more confident | Make protection more flexible | Accelerate your product success |
| Provide mature, well-tested and supportive security technologies. | Provide a variety of advanced physical security features for you to choose. | Rich IP products and sound ecosystem support can effectively reduce product development costs. |
| • Built on market proven technology that has been deployed in billions of SecurCore processors. • Get support from billions of Cortex-A-based devices using TrustZone technology. • Reuse existing knowledge on the same programmer model that has been deployed by millions of Cortex-M developers. | • Strengthen market adaptability for the widely familiar Cortex-M series without compromising performance. • Provides high flexibility and optional features for advanced features including signal processing. • Higher security (Lockstep, configurable parity, observability) for faster, lower-cost deployment of system security features. | • Optimize in our comprehensive Arm Security Solutions portfolio. • Easy upgrade from Cortex-M33 processor. • Reuse existing software built on Cortex-M devices. • Supported by the world's first embedded ecosystem, access to the world's largest open knowledge base. |
 Why prevent physical attacks?
Why prevent physical attacks?
We encounter more and more devices in our daily lives - such as at home, workplaces, hospitals, industrial sites, urban spaces, and so on - some of which are networked and some are not. Among these, many devices store valuable personal information, making them the targets of physical attacks. From a cost perspective, these attacks have become more feasible due to the deployment and presence of simple data collection tools. We have witnessed more and more physical attacks, such as side channel attacks have become part of the standard security threat model. The main concern for physical attacks comes from the scalability (harmful) factor of attack, that is, by attacking a device, the attacker can extract the source code and discover vulnerabilities, thus carrying out large-scale network attacks.
Yossi Oren, a senior lecturer at TechRepublic BGU, summarized in his IoT Security blog: “You only need to make one physical visit — once you have purchased a copy of a device or a model of a camera, and in the lab You successfully attack it and you get all the information you need to remotely attack the same device or model.â€
We use an analogy to explain why we developed the Cortex-M35P: it is like protecting your house. Since you have valuables in your house, it is vital to ensure that all entrances are protected and that the difficulty of a thief breaking into a particular entrance is taken into account.
Figure 1: Protecting equipment is as safe as protecting a house - the strength of security depends only on the weakest link!
For example, if a thieve wants to steal through a small window on the top floor, he may need a ladder and some special tools to succeed. Because this is very complicated and difficult to use, you may think that the small window on the top floor will not be the preferred entrance for burglary burglary and that valuables are protected. However, if there is a very valuable item in the house, or if you don't have to struggle to get into the window on the top floor, then the thief may have managed to get in.
This concept also applies to the Internet of Things. Arm has a wide range of security that can defend against various entry points. Now Arm is strengthening its defense against physical attacks. The Cortex-M35P has been developed to meet the needs of all market-adapted embedded and IoT markets. Now, any Cortex-M developer facing the requirements of a physical security project can upgrade to this latest Cortex-M processor without forcing all previous development efforts.
In addition, the processor can be matched with the rest of the Arm IP portfolio to form a powerful and comprehensive security solution that accelerates time-to-market. Developers can benefit from Arm's extensive ecosystem that offers the widest range of development tools, compilers, debuggers, operating systems, and software middleware that can save time and money.
 Physical attacks related to other types of attacks
Physical attacks related to other types of attacks
As the attack surface continues to grow and the scale of the Internet of Things (IoT) grows exponentially, it may be difficult to determine how to protect your next-generation devices based on the current situation during product design planning. In order to understand and address this situation, Arm describes security by modeling four different types of attack targets: communication, product life cycle, software and physical attacks, as shown in Figure 2. The risk to the device depends on the value of the application and the data. Many devices need to consider more attacks that target the underlying system, such as attacks on the underlying software, which can be fully protected by the isolation provided by Arm TrustZone. However, there are other types of devices that need to consider more complex attacks, such as the risk of physical attacks on the chip.
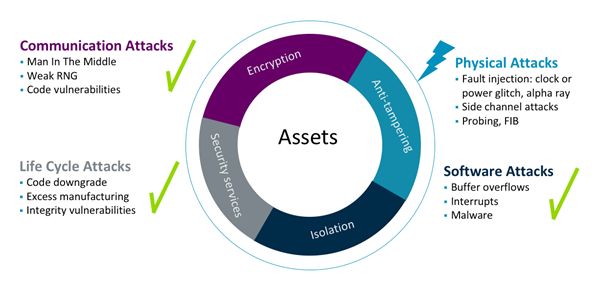
Figure 2: Evaluation of Threat Factors for Four Different Types of Security Attacks
Which attacks you need to protect depends on what physical attacks you think will pose an adequate threat to your product. The recommendation of the Arm PSA platform security architecture is that security always starts with analysis, where analysis refers to analysis using a threat modeling program. Through threat modeling, you can assess the security of your device and predict how it might be hacked or exploited. If the security realm is unfamiliar to you, then threat modeling may be a daunting process, so Arm created three completely free threat model examples.
When assessing the equipment and the threats it faces, an important next task is to take appropriate measures to protect your equipment. Arm recommends using a tiered security approach and using the right combination of countermeasures to implement different levels of protection for your equipment.
Arm expands a series of IPs to deal with all types of security threats. When physical attacks are considered to be sufficiently risky, you can choose to use processors that mitigate physical attacks. The Cortex-M35P provides a solution that combines software isolation and physical security to help designers achieve a higher level of system security against physical and software attacks. You may decide that you need to use a hardware-accelerated encryption mechanism to attack the Channel Attack (SCA) - and CryptoIsland-300P and CryptoCell-312P just can help in this area.
 Arm Cortex-M35P
Arm Cortex-M35P 
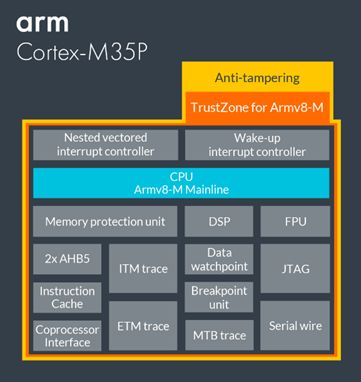
Physical protection
When the value of the protected asset is high enough, the hackers have enough incentive to take physical attacks on the device. The Cortex-M35P offers several specialized components to protect the device from such attacks.
The Cortex-M35P contains a number of security features that protect against physical attacks. The "non-differential timing" makes the number of cycles of any instruction operation constant, thereby preventing information leakage. Users can specify whether to activate this item.
Another example is 100% parity coverage. Each flip-flop in the processor is protected with configurable parity to detect random errors or purposeful error injection.
2. Instruction cache
Integrated cache improves performance when fetching from embedded Flash. Flash usually does not provide RAM-level access time, which is also a common performance bottleneck. This problem is solved by activating the optional internal cache. The information stored in the cache is also protected from physical attacks.
3. TrustZone: The foundation of system-wide security
TrustZone enhances the protection of information security-sensitive functions in the system. It provides software isolation of code, memory, and I/O while meeting the requirements of embedded applications: real-time, deterministic response, minimal switching overhead, and ease of software development.
The Cortex-M35P processor with TrustZone has two security states, namely, security and non-security status, and some features that are closely related to the two states, as shown in Figure 3:
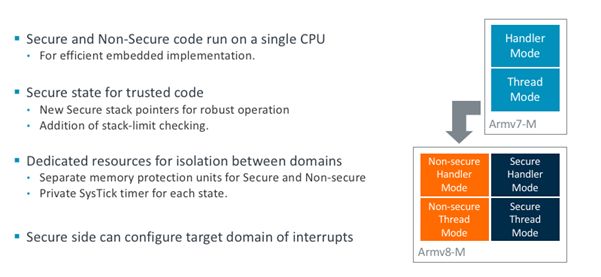
Figure 3: Armv8-M Extra Security Status
4. Memory Protection Unit (MPU) for Task Isolation
The increase in software reliability and system security can be achieved by allowing only a specific memory area required for each module to access the operation. As a complement to TrustZone, this protection prevents accidental access to critical data. Each security zone can be assigned a dedicated MPU and configure a different number of zones. It is also easier to program the domain, removing the constraint that the domain must be aligned to an integer power of two.
This optional MPU is programmable and can provide up to 16 regions for secure and non-secure states, respectively. In a multitasking environment, the operating system can reprogram the MPU during task context switching to define the memory access permissions for each task. For example, an application's tasks may be granted access to only certain application data and specific peripherals. In this way, the MPU can protect all other memories and peripherals from corrupted or unauthorized access, significantly improving system reliability.
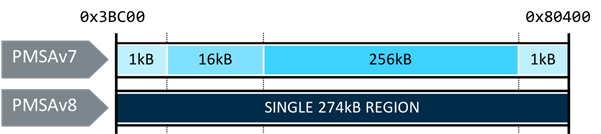
Memory area setup is easier
The Cortex-M35P internal protection architecture is based on the "protected memory system architecture (PMSA)" v8 version. This version uses the comparison with the base address and the termination address to define the scope of action, rather than the previous solution that must be aligned to an integer power-of-two address. Each zone has a basic start address, end address, access rights, and memory attribute settings. The result is that coverage of the target range can be accomplished using only one Region, rather than using multiple alignments connected to regions of different sizes as in the past. This greatly simplifies software development, encourages users to use the MPU more frequently, and reduces programming steps to reduce the number of context switches.
5. Extensible coprocessor interface
Dedicated computing can be very useful for specific applications. While achieving this expanded computing power, it is equally important to maintain all the advantages of the world’s leading ecosystem—the widest selection of development tools, compilers, debuggers, operating systems, and middleware.
The Cortex-M35P processor includes an optional dedicated bus interface for integrating tightly coupled accelerator hardware. For frequently used compute-intensive operations, this interface provides a mechanism to enhance general-purpose computing capabilities by custom processing hardware. Most importantly, it does not damage the ecosystem. This interface controls and data signals, supports up to 8 coprocessors, and provides processor privilege and security status as well as information on instruction types, associated registers, and operation fields.
6. Digital Signal Processing (DSP) expansion
In order to accelerate software development, Arm also provides a free DSP library in the CMSIS project. The library contains a series of digital filters, transformations and mathematical functions such as matrices, and supports a range of data types. The CMSIS project is an open source project, and the development version is released via GitHub.
The optional integer DSP extension adds 85 instructions. In most cases, DSP instructions can improve program performance by an average of three times, improving the performance of all applications with digital signal control at the core.
7. Floating Point Unit (FPU)
The optional FPv5 single-precision floating-point extension includes an additional 16 64-bit registers. This extension adds 45 IEEE754-2008 compatible single-precision floating-point instructions. Using floating-point instructions usually results in an average performance improvement of 10 times that of an equivalent software library. The FPU is included in a separate power domain, allowing power off when not enabled or not used.
In summary, physical attacks are one of several potential attacks on embedded or IoT devices. Arm's PSA platform security architecture assesses the level of security that designers need to pass through the threat modeling process in order to employ appropriate countermeasure combinations. Physical attacks are becoming simpler and cheaper, so advanced chip protection technology is crucial. However, physical security design is usually more complicated.
Arm's new physical security IP suite now provides market adaptability to any developer. The Arm Cortex-M35P processor provides an efficient security solution for software and physical attacks through TrustZone technology and tamper-proof features. Combining Arm CryptoCell IP, Arm CryptoIsland IP, or a specialized custom encryption solution with the support of the Arm ecosystem, developers of any embedded or IoT solution can ensure that they have a strong trusted foundation to perform Secure Internet of Things implementation deployment - because market adaptability is well underway.
aio desktop, aio computer, desktop all in one, all in one desktop computer, all in 1 pc, computer all in one pc
Guangdong Elieken Electronic Technology Co.,Ltd. , https://www.elieken.com