Since the global outbreak of ransomware in May, its amazing destructive power has affected hundreds of thousands of users in hundreds of countries and regions. Many companies have been forced to interrupt business or stop production, including Honda and Nissan. Car manufacturer.
On June 21, Nippon Co., Ltd. announced that the Sayama plant in Tokyo was shut down for one day due to the ransom virus. Honda is not the first car company to be attacked by ransom. As early as the extortion of the ransomware virus in May, Renault and Nissan received the ransom virus, resulting in the Renault-Nissan alliance in Japan, the United Kingdom, France, Suspension of production at several plants in Romania and India.
Although these "discontinued" enterprises have finally returned to normal operation, they have also sounded the alarm for more car companies: now the blackmail virus invades the factory, and the future car is intelligent and networked. The degree is getting higher and higher, and there are more and more components in the car's intranet. When more and more cars are connected on the road, will it directly attack the vehicle itself? In the face of an increasingly open car environment, how can car companies and related component manufacturers ensure the safety of car information? In the event of such attacks, how should the car companies or consumers respond? According to these scenarios that may arise in the future, many experts have recently adopted the theme of "Intelligent Networked Car Information Security" in China International Intelligent Networking Car. In-depth discussions were held at the Technical Annual Meeting (CICV 2017), in particular, for the main information security threats and corresponding solutions faced by intelligent networked vehicles, and published their own opinions.

Where are the most vulnerable to cyber attacks?
In September 2016, Tencent Cohen Labs announced that they successfully invaded the Tesla vehicle in a “remote without physical contact†manner to remotely control the vehicle's parking status and travel status. In April 2017, a network security company said that there were loopholes in the Hyundai Auto App, and that hackers could remotely launch Hyundai's cars. Hyundai confirmed the existence of this vulnerability. In June, software security engineer Jay Turla launched an open source cyber attack on Mazda Motors, enabling anyone to use a USB flash drive to execute malware code on Mazda vehicles... Many, such network security problems occur more and more frequently, it is especially necessary to master some of the necessary intelligent network security protection technologies for car companies and related component manufacturers.
So, how can we effectively prevent cars from being attacked by hackers? To answer this question, you must first figure out which areas of the intelligent networked car are the most vulnerable.
Wang Xinnan from the artificial intelligence room of the R&D department of the intelligent network car of FAW Technology Center believes that the attacks on the intelligent network car system mainly come from two aspects - internal attack and long-range attack. Among them, the internal attacks are mainly caused by the defects of the intelligent network connection, such as the lack of security of the bus, the gateway, the ECU, etc. Specifically, there are local attacks on the ECU nodes on the bus by exploiting the vulnerabilities on the bus. Kind.
The long-range attack is mainly caused by the continuous improvement of the network and the intelligence of the automobile. The communication channels between the automobile and the outside become more and more, which increases the security risk. According to different attack points, it is also divided into multiple situations, such as indirect physical access attacks through USB ports, CD players, OBD ports, etc., or short-range wireless access attacks through mobile phones, Bluetooth, V2X communication, cameras, etc. And use WEB browsing, telephone communication to carry out long-distance direct attacks, and one is through the App store for long-distance indirect attacks.
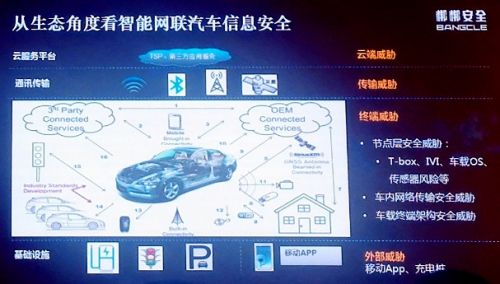
Liu Ding, a senior security researcher, is similar to the above. He believes that in the future, intelligent networked vehicles will face 12 information security threats from the cloud, transmission, terminal and external levels. The cloud is mainly stored in the cloud. The data of the platform is maliciously stolen, falsified, or destroys the integrity of the data; when the car communicates with the outside world through the "VX" technology, if the network is encrypted and authenticated insufficiently, it is easy for the attacker to induce the vehicle to occur by using the pseudo message. Misjudgment affects automatic vehicle control; terminal node threat refers to attack through T-BOX, terminal upgrade, vehicle OS, sensor, in-vehicle network transmission, vehicle terminal architecture, etc. Finally, the external threat mainly comes from mobile APP or through charging pile. Information is related to the attack. It can be seen that at the point where the intelligent networked car is vulnerable to attack, everyone basically reached an agreement, but the statement is different.
Cyber ​​attacks "everywhere" How to see the move?
With the increasing level of intelligent and networked vehicles, the types and quantities of vehicle terminals have increased substantially, and the number of cyber attacks that can be implemented on automobiles has increased. Although the current car attacks on cyber attacks are only a few cases, they have not been as massive as the "blackmail virus", causing adverse effects, and it should not be underestimated. In particular, at present, intelligent networked cars are gradually mass-produced, and car manufacturers and related component manufacturers must consider in advance and formulate preventive measures.
As a representative of vehicle manufacturers, FAW, in response to car network attacks, according to Wang Yinan's introduction is mainly based on the different functional areas to develop appropriate protective measures. He believes that intelligent networked cars can be divided into four different functional areas, namely basic control function areas, such as sensing unit, chassis system, etc.; extended function areas, such as telematics, infotainment management, car body System, etc.; external interfaces, such as LTE-V, Bluetooth, WIFI, etc.; and external functional areas such as mobile phones, memories, various diagnostic instruments, and cloud services. Each functional area has different definitions and requirements for security. It is necessary to define a reasonable and standardized system architecture, isolate different functional areas, and strictly control information flow between different areas, including access authentication and data encryption. To ensure the safe transmission of information, so as to achieve the high availability, convenience and privacy of the intelligent driving function.
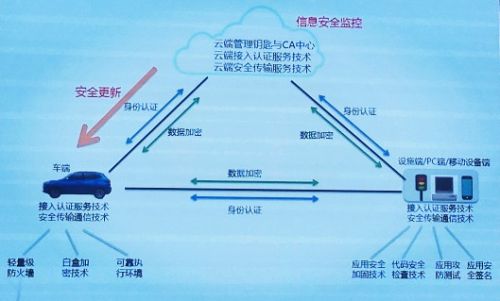
In this process, the T-BOX serves as one of the interfaces between the car and the external network, ensuring its safety is of paramount importance. Wang Weinan believes that car companies can start from the perspective of identity authentication, data security, gateway and firewall, key management, firmware security, etc. to create a secure T-BOX system. In addition, there are background servers, mobile APPs, and OTAs. It is also necessary to develop corresponding anti-attack measures according to different work scenarios. However, regardless of which component, identity authentication and data security are the most basic requirements.
Lu Xinhong, a car safety consultant from Qihoo 360, advises car companies to ensure the safety of their cars from Security to Safety. He believes that at this stage, the most important cybersecurity risk facing cars comes from the rapid iteration of hacker technology, while car companies compare professional information security organizations, security management mechanisms, necessary security technologies and security operations personnel. Lack of, so we need to start from various aspects of information security operations, technology, strategy, etc., to develop preventive measures.
Specifically, the whole life cycle safety guarantee is implemented in six stages, which are the project planning stage. At this stage, it is necessary to comprehensively analyze the safety risks faced by the vehicle network and plan the safety route. In the engineering design stage, the main control products of the supplier. Security, enhance the access rights of the vehicle network, and ensure the security of the network environment and the security of remote control; in the sample production stage, the vehicle security problem can be discovered in time through the implementation of the security check mechanism; the main task is to evade the test and evaluation stage. Pre-marketing vehicle networking platform and vehicle safety issues; in the mass production phase, safety tools can be tested in batches through tools; in the product delivery phase, it is mainly to provide early warning for security attacks and to monitor and operate vehicle safety throughout the country. In this way, the corresponding precautions are specified at each stage to improve vehicle safety.
Technical protection, of course, important regulatory support is also essential
Of course, in order to better protect against network security, in addition to the efforts of car companies and component manufacturers, policy norms and guidelines are also indispensable. According to Professor Luo Lei of the University of Electronic Science and Technology, there are already relevant guidance documents at home and abroad. For example, in October 2016, the US Highway Traffic Safety Administration issued a "Modern Automotive Information Security Best Practices", which is followed by the "Automotive Driving Policy" released in September 2016 for intelligent networked vehicles. Another important guidance document issued, which provides guidance on the safety related work of the automotive industry from two perspectives, namely the general network security guidance and the network security guidance for the automotive industry.
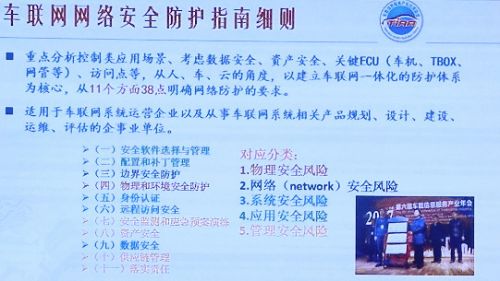
In China, the intelligent network alliance automobile industry technology innovation strategic alliance was established, and the automobile network and information security were taken as the focus of attention, and the relevant intelligent network connection work was carried out through the National Automobile Standardization Committee. In addition, in February of this year, the In-vehicle Information Service Industry Application Alliance also released the first white paper on network security in China, which introduced the development of security, challenges and future development of domestic vehicle network. Also released together is the "Regulations on the Safety Protection of Vehicle Networking (Consultation Draft)", which is based on the "Network Security Law of the People's Republic of China" and the integration of the industry development of the Internet of Vehicles. The protection system is the core, and the requirements for network protection are clearly defined from 38 aspects in 11 aspects, which is of great reference significance.
Summary of the world: At present, the network of automobiles is becoming more and more open, and more and more places are vulnerable to cyber attacks by criminals. In this context, it is necessary to build a safe intelligent network connection environment, car enterprises and terminals. And component manufacturers must start from the three levels of end, pipe, and cloud, and formulate reasonable preventive measures according to the characteristics of each level. In addition, the intelligent network connection vehicle information security standards and guidance norms at the level of laws and regulations are also indispensable. Only when such a multitude of parties work together, technology and regulations go hand in hand, and actively promote the development of automotive information security technology, it is expected that in the future, after the large-scale landing of intelligent networked vehicles, it will be away from attacks such as ransomware and become our real “travel assistantâ€!
External Cavity Tunable Laser,Laser Grating Sensor,Bragg Grating Stabilized Laser,Grating Stabilized Diode Laser
AcePhotonics Co.,Ltd. , https://www.acephotonics.com